Ring Topology Advantages and Disadvantages: The concept of topology is derived from the Greek words ‘topos’ and ‘logos,’ where the work ‘topo’ implies ‘place’ and ‘logos’ indicates ‘study.’ In the subject of computer networks, we use topology to explain in what way a network is physically correlated and also explain the logical stream of information in the network. A topology principally describes how network devices are interlinked and their interaction with each other using various communication links.
Students can also find more Advantages and Disadvantages articles on events, persons, sports, technology, and many more.
Computer networks are constructed based on two types of network topologies as defined below, explicitly:
- Physical Topology: A physical topology explains how the computers or the network nodes connect in a computer network. It organizes various elements such as links, nodes, and other devices, including the location and code installation of a computer network. In simple words, it is the physical arrangement of workstations, nodes, and cables in the network.
- Logical Topology: A logical topology represents the flow of data from one computer to another computer. It is connected to a network protocol and describes how the system moves data throughout the network and the path it takes. In simple words, it is how the devices communicate internally. Network topology describes the organization or structure of the computer network physically and logically. A network can be comprised of one or more physical topologies and multiple logical topologies simultaneously.
What is Meant by Ring Topology?
Each host machine connects to two other devices in a ring topology that creates a circular network model. When one host tries to communicate or send a message to a non-adjacent host, the data moves through all intermediate hosts and finally reaches the desired host.
The administrator might need only one extra cable to connect with one more host in the existing node structure.
The failure of any host results in the loss of the whole ring topology. Thus, every connection in the ring topology is a point of failure. Due to this reason, some methods apply one more backup ring.
In this article, the advantages and disadvantages along with the features and some frequently asked questions about ring topology are discussed in detail.
Significant Features Of The Ring Topology
- It is incredibly reliable for long-distance communication as each node in the network acts as a repeater. Therefore, the signal does not lose its strength.
- The built-in acknowledgment device is available in a ring topology is released only when the network completes communication.
- The use of tokens prohibits the chance of cross-communication or collisions because only one device has charge of the network, and two devices are allowed to communicate concurrently.
- Ring Topology can be used to enhance the fidelity of communication links moreover. If one link breaks, then the other is prepared for communication.
This article contains a detailed description of the following:
- The Advantages of Ring Topology
- The Disadvantages of Ring Topology
- A Comparison Table for the Advantages and Disadvantages of Ring Topology
- FAQS Pros and Cons of Ring Topology
Advantages of Ring Topology
- Execution: By executing you can achieve a ring topology network with less effort. Devices can be arranged one after the other without a specific number. There are no limitations to the number of devices that you can place. Whenever you add fresh devices, you only need to move the adjoining device.
- Administration: High-speed data transfer rates are another classic feature of a ring network topology. The data transmission that occurs between each workstation generally is quite fast here. Even under the condition of heavy load, interruptions will not impact its performance.
- Adaptability: The construction of ring topology makes the adaptability of devices straightforward. Users can keep adding workstations, and it will still not cause any performance delays or problems in the network.
- Fidelity: Even though ring topology requires hardiness, it can still be quite reliable for use to some extent. Mainly by using a set of multiple rings. The bidirectional characteristic of the ring topology guarantees that there are very few failures. The data moves in two directions in a ring topology, and therefore, for the same node, various paths are used.
- Direction of the Data: The ring topology’s one-direction data flow ensures scarce chances of data collisions. Hence, the data transfer process is more fluid here.
- Server Specifications: Since all workstations are connected circularly, there is no need for network servers. Therefore, each workstation on the ring topology has its unique connectivity. The only element necessary here is the use of special cables to connect each device on the topology structure.
- Troubleshooting Feature: Unless one-directional, troubleshooting and error in a ring topology are relatively straightforward.
In the case of any failure, all the workstations placed after the malfunctioning computer will quit working. Hence, users can spend less time classifying the place of network failure.
Disadvantages of Ring Topology
- Expense: Ordinarily, a ring topology architecture needs expensive hardware components for establishing the network. Without the proper cables and network cards, you cannot link the workstations, making the installation process pretty high. Hence, for users with a fixed budget, it is desirable to try some other options.
- Activity Rate: Even though ring topologies maintain a high-speed data transfer rate, it is still more leisurely than a star topology. When the data transfers from one device to another, it passes through every workstation, which causes a lag in the time while the data reach its destination. Therefore, the whole network activity rate is slowed.
- Protection: In the system of ring topology, data passes through each workstation attached. Every workstation connected can access information of the other station, which creates some privacy issues considering unauthorized individuals who can easily interrupt sensitive information of users.
- Hardiness: The path taken by most of the ring topology network users is one-directional, which basically means that each device is interdependent. In the case of a single workstation breakdown, the entire network will collapse.
- Device Attachment: When a new node is attached or disconnected from the existing ring topology, it causes disturbances in the network activity. Every workstation on a ring topology is interlinked, which means that users need to bear the trouble of breaks or breakdowns during network changes.
- Cable Breakdown: The entire network in a ring topology depends heavily on a single cable. Several network nodes are placed circularly on this cable. By accident, if the connector experiences any failure, the signals will face a blockage and stop traveling.
- Bandwidth Deficiencies: Ring topology is minimal when it comes to bandwidth. If there are multiple devices connected, that could create bandwidth deficiencies.
As a result, the users may experience communication impediments, which is why it is advisable to make sure that there are few nodes connected in a ring topology.
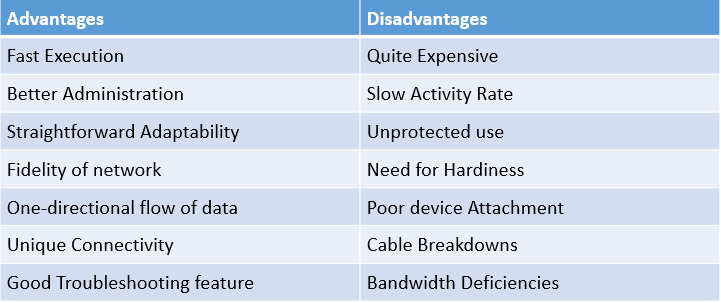
Ring Topology Advantages And Disadvantages In Tabular Form
| Advantages | Disadvantages |
|---|---|
| Efficient Data Transfer | Limited Scalability |
| No Collisions | Single Point of Failure |
| Easy to Install and Expand | Difficult to Troubleshoot |
| Fault Tolerance | Lower Bandwidth |
| Cost-Effective | Delay in Data Transmission |

A Comparison Table for Advantages and Disadvantages of Ring Topology
| Advantages | Disadvantages |
| Fast Execution | Quite Expensive |
| Better Administration | Slow Activity Rate |
| Straightforward Adaptability | Unprotected use |
| Fidelity of network | Need for Hardiness |
| One-directional flow of data | Poor device Attachment |
| Unique Connectivity | Cable Breakdowns |
| Good Troubleshooting feature | Bandwidth Deficiencies |
FAQ’s Pros and Cons of Ring Topology
Question 1.
Where can I use Ring Topology?
Answer:
In WAN and MAN, a ring topology is used as the backbone to connect the customers. The Ring is bidirectional and has two distinct routes to the public switch.
Question 2.
What happens if a Ring topology fails?
Answer:
A single node failure or cable breakdown can separate every node attached to the Ring. Therefore, very thoroughly arranged networks where every device can access the token and the opportunity to transmit data may break down if one node stops working.
Question 3.
What is a good example of ring topology?
Answer:
Token Ring is a good example of ring topology.
