CBSE Sample Papers for Class 12 Computer Science Paper 1 is part of CBSE Sample Papers for Class 12 Computer Science. Here we have given CBSE Sample Papers for Class 12 Computer Science Paper 1.
CBSE Sample Papers for Class 12 Computer Science Paper 1
| Board | CBSE |
| Class | XII |
| Subject | Computer Science |
| Sample Paper Set | Paper 1 |
| Category | CBSE Sample Papers |
Students who are going to appear for CBSE Class 12 Examinations are advised to practice the CBSE sample papers given here which is designed as per the latest Syllabus and marking scheme as prescribed by the CBSE is given here. Paper 1 of Solved CBSE Sample Paper for Class 12 Computer Science is given below with free PDF download Answers.
Time: 3 Hours
Maximum Marks: 70
General Instructions
- All questions are compulsory within each Section.
- Programming Language in SECTION A : C++.
- Answer the questions after carefully reading the text.
SECTION A
Question 1.
(a) Write the type of C + + tokens (keywords and user-defined identifiers) from the following:
(i) new
(ii) While
(iii) case
(iv) Num_2
(b) Anil typed the following C++ code and during compilation, he found three errors as follows:
(i) Function strlen should have prototype
(ii) Undefined symbol cout
(iii) Undefined symbol endl
On asking, his teacher told him to include necessary header files in the code. Write the names of the header files, which Anil needs to include, for successful compilation and execution of the following code:
void main()
{
char Txt[] = "Welcome":
for (int C=0; C<strlen(Txt); C++)
Txt[C] = Txt[C]+1;
cout<<Txt<<endl:
}(c) Rewrite the following C++ code after removing any/all syntactical errors with each correction underlined.
Note: Assume all required header files are already being included in the program.
void main()
{
cout<<"Enter an Alphabet:": cin>>CH;
switch(CH)
case 'A' cout<<"Ant"; Break;
case 'B' cout<<"Bear"; Break:
}(d) Find and write the output of the following C++ program code: Note Assume all required header files are already included in the program.
#define Diff(N1, N2) ((N1>N2)?N1-N2:N2-N1)
void main()
{
int A, B, NUM[] = {10, 23, 14, 54, 32};
for(int CNT=4; CNT>0: CNT--)
{
A=NUM[CNT];
B=NUM[CNT-1]:
cout<<Diff(A,B)<<'#':
}
}(e) Find and write the output of the following C++ program code:
Note Assume all required header files are already being included in the program.
void main()
{
int *Point. Score[]={100, 95, 150, 75, 65, 120};
Point = Score:
for(int L = 0: L<6; L++)
{
if((*Po1nt)*10==0) *Point /= 2;
else
*Point -= 2;
if((*Point)*5==0)
*Point /= 5;
Point++;
}
for(int L = 5; L>=0; L--)
cout<<Score[L]<<"*";
}(f) Look at the following C++ code and find the possible outputs (s) from the options (i) to (iv) following it. Also, write the maximum values that can be assigned to each of the variables N and M.
Note:
- Assume all the required header files are already being included in the code.
- The function random(n) generates an integer between 0 and n-1.
void main()
{
randomize();
int N=random(3), M=random(4);
int D0CK[3][3] = {{1, 2, 3}, {2, 3, 4},{3, 4, 5}};
for(int R=0; R<N; R++)
{
for(int C=0: C<M; C++)
cout<<DOCK[R][C]<<" ";
cout<<endl;
}
}
Question 2.
(a) Differentiate between protected and private members of a class in context of Object Oriented Programming. Also, give a suitable example illustrating accessibility/non-accessibility of each using a class and an object in C + +.
(b) Observe the following C++ code and answer the questions (i) and (ii).
Note: Assume all necessary files are included.
class TEST
{
long TCode:
char TTitle[20];
float Score;
public:
TEST() //Member Function 1
{
TCode = 100;
strcpy(TTitle. "FIRST Test");
Score=0;
}
TEST(TEST &T) //Member Function 2
{
TCode=E, TCode+1;
strcpy(TTitle, T.TTitle);
Score=T. Score;
}
};
void main()
{
................ //Statement 1
................ //Statement 2
}(i) Which Object Oriented Programming feature is illustrated by the Member Function 1 and the Member Function 2 together in the class TEST?
(ii) Write Statement 1 and Statement 2 to execute Member Function 1 and Member Function 2 respectively.
(c) Write the definition of a class BOX in C++ with the following description:
Private Members
-BoxNumber // data member of integer type
-Side // data member of float type
-Area // data member of float type
-ExecArea() // Member function to calculate and assign Area as Side * Side
Public Members
-GetBox() // A function to allow user to enter values of
// BoxNumber and Side. Also, this
// function should call ExecArea() to Calculate Area
-ShowBox()
// A function to display BoxNumber. Side and Area
(d) Answer the questions (i) to (iv) based on the following:
class First
{
int X1;
protected:
float X2;
public:
First():
void Enter1();
void Display1();
};
class Second : private First
{
int Y1;
protected:
float Y2;
public:
Second();
void Enter2();
void Display();
};
class Third : public Second
{
int Z1;
public:
Third():
void Enter3();
void Display();
};
void main()
{
Third T; //Statement 1
...............; //Statement 2
}(i) Which type of Inheritance out of the following is illustrated in the above example?
Singel Level Inheritance, Multilevel Inheritance, Multiple Inheritance
(ii) Write the names of all the member functions, which are directly accessible by the object T of class Third as declared in main() function.
(iii) Write Statement 2 to call function Display() of class Second from the object T of class Third.
(iv) What will be the order of execution of the constructors, when the object T of class Third is declared inside main()?
Question 3.
(a) Write the definition of a function AddUp(int Arr[ ], int N) in C++, in which all even positions (i.e. 0, 2, 4,….) of the array should be added with the content of the element in the next position and odd positions (i.e. 1, 3, 5,……) elements should be incremented by 10.
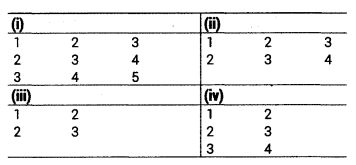
Example: if the array Arr contains
![]()
Then the array should become
![]()
Note:
- The function should only alter the content in the same array.
- The function should not copy the altered content in another array.
- The function should not display the altered content of the array.
- Assuming, the Number of elements in the array are Even.
(b) Write a definition for a function SUMMIDCOL(int MATRIX[ ] [10], int N, int M) in C++, which finds the sum of the middle column’s elements of the MATRIX (Assuming N represents number of rows and M represents number of columns, which is an odd integer).
Example: If the content of array MATRIX having N as 5 and M as 3 is as follows:

The function should calculate the sum and display the following:
Sum of Middle Column: 15
(c) ARR[15] [20] is a two-dimensional array, which is stored in the memory along the row with each of its elements occupying 4 bytes. Find the address of the element ARR[5][15], if the element ARR[ 10] [5] is stored at the memory location 35000.
(d) Write the definition of a member function PUSHGIFT() for a class STACK in C++, to add a GIFT in a dynamically allocated stack of GIFTs considering the following code is already written as a part of the program:
struct GIFT
{
int GCODE; //Gift Code
char GDESC[20]: //Gift Description
GIFT *Link;
};
class STACK
{
Gift * T0P; .
public:
STACK()
{
T0P=NULL;
}
void PUSHGIFT():
void POPGIFT();
~STACK();
};(e) Convert the following Infix expression to its equivalent Postfix expression, showing the stack contents for each step of conversion:
X – (Y + Z)/U * V
Question 4.
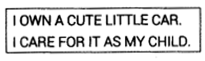
(a) Polina Raj has used a text editing software to type some text in an article. After saving the article as MYNOTES.TXT, she realized that she has wrongly typed alphabet K in place of alphabet C everywhere in the article.
Write a function definition for PURETEXT() in C++ that would display the corrected version of the entire article of the file MYNOTES. TXT with all the alphabets “K” to be displayed as an alphabet “C” on screen.
Note: Assuming that MYNOTES. TXT does not contain any C alphabet otherwise.
Example:
If Polina has stored the following content in the file MYNOTES.TXT:
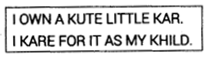
The function PURETEXT() should display the following content:
(b) Write a definition for function COUNTPICS( ) in C++ to read each object of a binary file PHOTOS.DAT, find and display the total number of PHOTOS of type PORTRAIT. Assume that the file PHOTOS.DAT is created with the help of objects of class PHOTOS, which is defined below:
class PHOTOS
{
int PCODE;
char PTYPE[20]; //Photo Type as "PORTRAIT", "NATURE"
public:
void ENTER()
{
cin>>PC0DE; gets (PTYPE);
}
void SHOWCASE()
{
cout<<PC0DE<<": "<<PTYPE<<endl:
}
char *GETPTYPE() {return PTYPE;}
};(c) Find the output of the following C++ code considering that the binary file CLIENTS.DAT exists on the hard disk with a data of 200 clients:
class CLIENTS
{
int CCode; char CName[20]:
public:
void REGISTER();
void DISPLAY();
};
void main()
{
fstream File;
File.open("CLIENTS.DAT", ios: :binary | ios::in);
CLIENTS C;
File.seekg(6*sizeof(C));
File.read((char*)&C, sizeof(C));
cout<<"Client Number: "<<File.tellg()/sizeof(C)+1;
File.seekg(0, ios::end);
cout<<"of "<<File.tellg()/sizeof(C)<<endl;
File.close();
}SECTION B
Question 5.
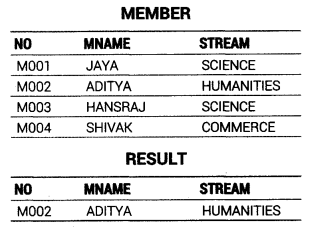
(a) Observe the following table MEMBER carefully and write the name of the RDBMS operation out of (i) SELECTION (ii) PROJECTION (iii) UNION (iv) CARTESIAN PRODUCT, which has been used to produce the output as shown in RESULT. Also, find the Degree and Cardinality of the RESULT:
(b) Write SQL queries for (i) to (iv) and find outputs for SQL queries (v) to (viii), which are based on the tables.
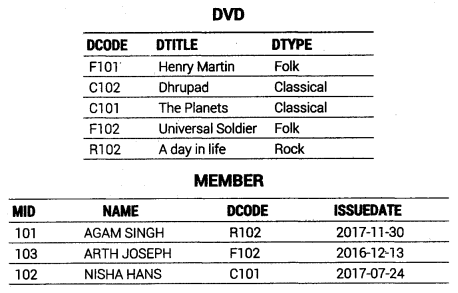
(i) To display all details from the table MEMBER in descending order of ISSUEDATE.
(ii) To display the DCODE and DTITLE of all Folk Type DVDs from the table DVD.
(iii) To display the DTYPE and number of DVDs in each DTYPE from the table DVD.
(iv) To display all NAME and ISSUEDATE of those members from the table MEMBER who have DVDs issued (i.e., ISSUEDATE) in the year 2017.
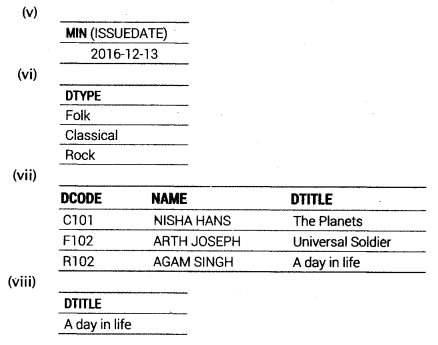
(v) SELECT MIN (ISSUEDATE) FROM MEMBER;
(vi) SELECT DISTINCT DTYPE FROM DVD;
(vii) SELECT D.DCODE, NAME, DTITLE
FROM DVD D, MEMBER M WHERE D. DC0DE=M.DCODE;
(viii) SELECT DTITLE FROM DVD
WHERE DTYPE NOT IN ("Folk", "Classical");Question 6.
(a) State DeMorgan’s Laws of Boolean Algebra and verify them using truth table.
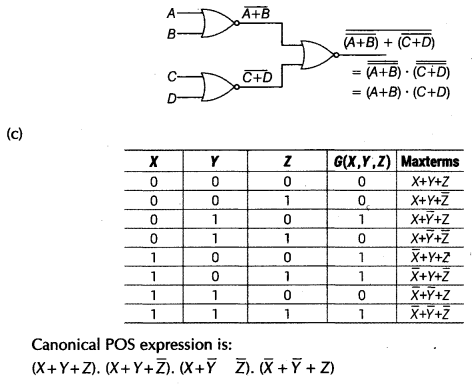
(b) Draw the Logic Circuit of the following Boolean Expression using only NOR Gates
(A+B).(C+D)
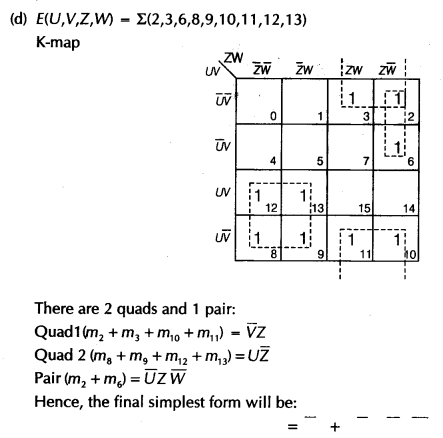
(c) Derive a Canonical POS expression for a Boolean function G, represented by the following truth table:
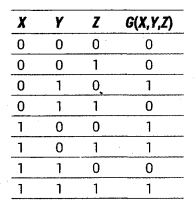
(d) Reduce the following Boolean Expression to its simplest form using K-Map:
E (U, V, Z, W) = Σ (2, 3, 6, 8, 9, 10, 11, 12, 13)
Question 7.
(a) Differentiate between communication using Optical Fibre and Ethernet Cable in context of wired medium of communication technologies.
(b) Janish Khanna used a pen drive to copy files from his friend’s laptop to his office computer. Soon his computer started abnormal functioning. Sometimes it would restart by itself and sometimes it would stop different applications running on it. Which of the following options out of (i) to (iv), would have caused the malfunctioning of the computer? Justify the reason for your chosen option:
(i) Computer Virus
(ii) Spam Mail
(iii) Computer Bacteria
(iv) Trojan Horse
(c) Ms. Raveena Sen is an IT expert and a freelancer. She recently used her skills to access the Admin password for the network server of Super Dooper Technology Ltd. and provided confidential data of the organization to its CEO, informing him about the vulnerability of their network security. Out of the following options (i) to (iv), which one most appropriately defines Ms. Sen?
Justify the reason for your chosen option:
(i) Hacker
(ii) Cracker
(iii) Operator
(iv) Network Admin
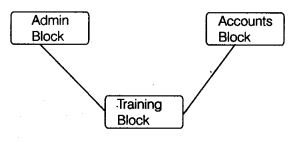
(d) Hi-Standard Tech Training Ltd. is a Mumbai based organization which is expanding its office set-up to Chennai. At Chennai office compound, they are planning to have 3 different blocks for Admin, Training, and Accounts related activities. Each block has a number of computers, which are required to be’ connected in a network for communication, data and resource sharing.
As a network consultant, you have to suggest the best network related solutions for them for issues/problems raised by them in (i) to (iv), as per the distances between various blocks/locations and other given parameters.
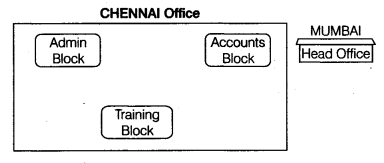
Shortest distances between various blocks/locations:
Number of computers installed at various blocks are as follows:
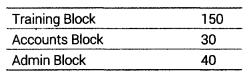
(i) Suggest the most appropriate block/location to house the SERVER in the CHENNAI office (out of the 3 blocks) to get the best and effective connectivity. Justify your answer.
(ii) Suggest the best-wired medium and draw the cable layout (Block to Block) to efficiently connect various blocks within the CHENNAI office compound.
(iii) Suggest a device/software and its placement that would provide data security for the entire network of the CHENNAI office.
(vi) Suggest a device and the protocol that shall be needed to provide wireless Internet access to all smartphone/laptop users in the CHENNAI office.
Answers
Answer 1.
(a) (i) new → keyword
(ii) While → user defined identifier
(iii) case → keyword
(iv) Num_2 → user defined identifier
(b) For strlen →
For cout, endl →
(c) correct code is:
void main()
{
char CH;
cout<<"Enter an Alphabet:"; cin>>CH;
switch(CH)
{
case 'A': cout<<"Ant"; break;
case 'B': cout<<"Bear"; break;
}
}(d) Output
22#40#9#13#
(e) Given program will give error, i.e. Multiple declaration for ‘L’.
If we remove int from 2nd for loop then output will be:
12*63*73*15*93*10*
(f) Possible Outputs: (ii) and (iii)
Maximum value of N is 2.
Minimum value of N is 0.
Maximum value of M is 3.
Minimum value of M is 0.
Answer 2.
(a) Private visibility A member declared as private can be accessed only in class. It cannot be accessed outside the class.
Protected visibility A member declared as protected can be accessed inside the class as well as outside the class that is subclass of the class in which member is declared.
e.g. class Super
{
private:
int x;
protected:
int y;
};
Class Sub : protected Super
}
private:
int z;
public:
void disp()
{
cout<<x<<y<<z;
/*Here y and z can be accessed but x cannot be accessed because it is a private member of Super class */
}
};(b) (i) Constructor overloading feature is illustrated by the Member Function 1 and the Member Function 2 together in the class TEST.
(ii) Statement 1
TEST T1; //To execute Member Function 1
Statement 2
TEST T2 = T1; //To execute Member Function 2
(c) class Box
{
int BoxNumber;
float Side, Area:
void ExecArea()
{
Area = Side*Side;
}
public:
voidGetBox()
{
cout<<"Enter the values of BoxNumber and Side";
cin>>BoxNumber;
cin>>Side;
ExecArea();
}
void ShowBox()
{
cout<<"BoxNumber: "<<BoxNumber<<endl;
cout<<"Side:"<<Side<<endl;
cout<<"Area: "<<Area;
}
};(d) (i) Multilevel Inheritance
(ii) Enter3( ), Display( ) of class Third, Enter2( ),
(iii) Statement 2
T.Second::Display( );
(iv) First() → Second() → Third()
Answer 3.
(a) void AddUp(int Arr[], int N)
{
for(int i=0; i<N; i++)
{
if(i*2==0)
Arr[i]+ = Arr[i+1];
else
Arr[i] + = 10;
}
}(b) void SUMMIDCOL(int MATRIX[ ][10], int N, int M)
{
int j, SUM=0;
j=M/2:
for(int i=0: i<N; i++)
SUM += MATRIX [i][j];
cout<<"SUM of Middle Column :"<<SUM;
}(c) B = 35000, W = 4 bytes, R = 15, C = 20,
Lr = 10, Lc = 5, I = 5, J = 15
For row-wise allocation,
Address of ARR[I][J] = B+W[C(I – Ir) + (J – Ic)]
ARR[5][15] = 35000 + 4[20(5 – 10) + (15 – 5)]
= 35000+ 4[20(-5) +10]
= 35000 + 4[-100+10]
= 35000 + 4[-90]
= 35000 – 360
= 34640
(d) void PUSHGIFT( )
{
GIFT *G = new GIFT;
cout<<"Enter gift code and description";
cin>>G->GCODE;
gets(G->GDESC);
if (TOP == NULL)
{
TOP = G:
}
else
{
G->Link = TOP
TOP = G;
}
}(e) The infix Expression is (X – (Y + Z) / U * V)
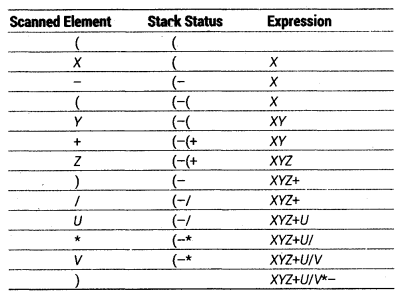
Postfix expression would be XYZ + U/V*-
Answer 4.
(a) void PURETEXT()
{
fstream fpl;
fpl. open("MYNOTES.txt", ios::in | ios::out):
if(!fpl)
{
cout<<"Cannot open file"<<endl;
exit(0);
}
char ch; .
char c;
while(!fpl.eof())
{
c=fpl.get();
if(c=='K')
{
fpl.seekg(-1, ios::cur);
fpl.put('C'):
}
}
fp1.clear();
fp1.seekp(0, ios::beg);
cout<<"\n After replacing character\n");
while(!fpl.eof())
{
fp1.get(ch);
cout<<ch;
}
fpl.close();
}(b) void COUNTPICS( )
{
int count = 0;
PHOTOS obj;
ifstream fpl; .
fp1.open("PHOTOS.DAT", ios::binary);
while (fpl.read((char*)&obj. sizeof(obj)))
{
if(strcmp(obj.GETPTYPE(),"PORTRAIT")==0)
count++;
}
cout<<"The total number of PHOTOS of type PORTRAIT is "<<count;
fpl.close();
}(c) Output
Client Number: 8 of 200
Answer 5.
(a) (i) SELECTION
Degree of table RESULT = 3
Cardinality of table RESULT = 2
(b) (i) SELECT * FROM MEMBER ORDER BY ISSUEDATE DESC; (ii) SELECT DCODE. DTITLE FROM DVD WHERE DTYPE = "Folk"; (iii) SELECT DTYPE, COUNT (*) FROM DVD GROUP BY DTYPE; . (iv) SELECT NAME, ISSUEDATE FROM MEMBER WHERE ISSUEDATE LIKE '2017%';
Answer 6.
(a) DeMorgan’s Laws of Boolean Algebra
DeMorgan’s laws are extremely useful in simplifying expressions in which a product or sum of variables is inverted. The two DeMorgan’s laws are:
(i) \(\bar { XY } =\bar { X } +\bar { Y }\) This law expressed as the complement of a product is equal to sum of complements, i.e. complement of two or more variables used in AND gate is same as the OR of the complement of each individual variable.
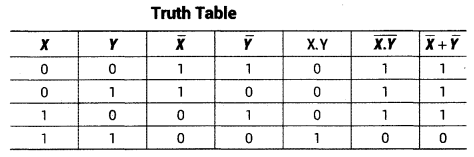
Both the columns. \(\bar { XY }\) and \(\bar { X } +\bar { Y }\) are identical, Hence Proved.
(ii) \(\bar { XY } =\bar { X } \bar { Y }\) This theorem expressed as the complement of sum is equal to the product of complements, i.e. complement of two or more variables used in OR gate is same as the AND of the complements of each individual variable.
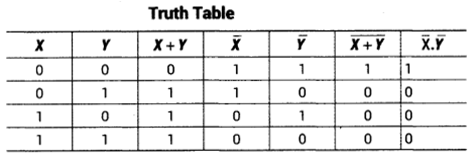
Both the columns \(\bar { XY }\) and \(\bar { X } \cdot \bar { Y }\) are identical, Hence Proved.
(b) Logic circuit for (A + B).(C + D):
Answer 7.
(a) Differences between Optical Fibre and Ethernet Cable are as follows:
| Optical Fibre | Ethernet Cable |
| These cables are made up of many thin strands of glass that transmit data using light signals. | These cables are comprised of multiple copper wires twisted together that transmit digital information using electrical signals. |
| Information sent via optical fiber cables is much more difficult to intercept because light can’t be read in the same way signals sent via copper cabling can be. | Due to the way in which data is transmitted across Ethernet copper cabling, it is vulnerable to being intercepted. Ethernet switches can help to improve security. |
| There are two kinds of optical fiber: single-mode and multi-mode. | There are two kinds of Ethernet cable: shielded pair and unshielded pair. |
(b) (i) Computer virus
Reason Computer virus can spread through external media such as CDs, pen drive etc. It is designed to infect the host program and gain control over the system without the owner’s knowledge.
(c) (ii) Cracker
Reason Crackers are generally responsible for breaking into networks, cracking passwords in websites and programs and generally causing havoc through the Internet.
(d) (i) Training Block is the most appropriate block/location to house the SERVER in the CHENNAI office to get the best and effective connectivity because it has maximum number of computers.
(ii)
(iii) Suggested device is firewall. And it will be placed where all messages are entering or leaving the entire network of the CHENNAI office.
(iv) Device: WiFi card
Protocol: TCP/IP
We hope the CBSE Sample Papers for Class 12 Computer Science Paper 1 help you. If you have any query regarding CBSE Sample Papers for Class 12 Computer Science Paper 1, drop a comment below and we will get back to you at the earliest.